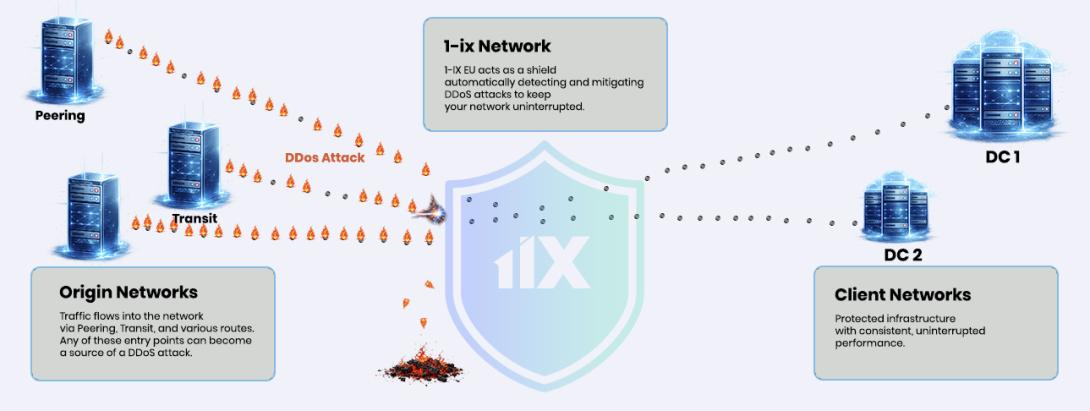
1-IX EU implements an automated DDoS Protection system designed to detect and mitigate attacks directly at the IXP layer, without requiring manual intervention from members.
System Overview
The system operates as a closed-loop detection and mitigation pipeline, combining traffic telemetry, behavioral analysis, and automated enforcement.
Core components:
- Traffic telemetry ingestion (sFlow / NetFlow)
- Baseline modeling (per member / per prefix traffic behavior)
- Anomaly detection
- Attack classification (by protocol, port, and traffic pattern)
- Mitigation decision engine
- Automatic rule deployment
Detection and Classification
The system continuously analyzes traffic across the exchange fabric and maintains behavioral baselines.
Detection is based on:
- Deviations from historical traffic patterns
- Sudden traffic spikes (volume or PPS)
- Protocol distribution anomalies
- Port-level distribution changes
- Flow entropy and concentration metrics
Once an anomaly is detected, traffic is classified into:
- Legitimate traffic
- Suspicious traffic
- Attack traffic
Classification is performed using multi-dimensional attributes, including:
- Source/destination IP distribution
- Transport protocol
- TCP/UDP ports
- Packet size patterns
- Flow characteristics
Mitigation
Mitigation is enforced automatically at the network level.
Supported actions:
- Traffic blocking (blackholing / discard)
- Rate-limiting (traffic shaping)
- Selective filtering based on protocol and port
- Whitelisting of legitimate traffic
Filtering capabilities include:
- IPv4 and IPv6 support
- Transport protocol matching
- Full TCP/UDP source and destination port matching
Rules are applied dynamically and can be adjusted or withdrawn automatically as traffic conditions change.
Automation Model
The system operates without requiring manual triggering.
Workflow:
- Traffic is continuously monitored
- An anomaly is detected
- Traffic is classified
- A mitigation strategy is selected
- Rules are deployed automatically
- Traffic is re-evaluated in real time
This enables:
- Rapid response to short-lived attacks
- Consistent mitigation across members
- Reduced dependence on manual NOC actions