Drop DDoS traffic
To help our customers mitigate the effects of Distributed Denial of Service (DDoS) attacks against their networks, we offer customer-triggered Advanced Blackholing (ADV_BH).
The current 1-IX Blackholing can completely block traffic to destination IP addresses under attack. However, this takes the destination completely offline and means the attacker wins.
With the Advanced Blackholing service, you can now block specific types of IP packets, including TCP / UDP / ICMP source and destination ports.
Advanced Blackholing requires an initial analysis of the attack. You need to identify the target IP(s) and, ideally, the exact traffic signature (protocol, ports).
Most DoS/DDoS attacks are based on a single traffic vector, such as UDP or TCP traffic on specific ports. After identifying the attack vector, select the appropriate community or communities from the tables below.
Blackholing via the route servers
- Customers advertise their IP/IPv6 prefix(es) tagged with the BGP BGP ADV_BH Community (target:50263:42xxxxxxxx) or (50263:667..677)
- Accepted prefix length by the 1-IX EU Route-Servers is /32 for IPv4 (only if ADV_BH is set)
- Accepted prefix length by the 1-IX EU Route-Servers is /128 for IPv6 (only if ADV_BH is set)
- Prefix validation (RIR and RPKI filtering) is applied as usual, to prevent unauthorized Blackholing
- The 1-IX EU Route Servers rewrite the next-hop of the advertised IP/IPv6 prefix(es) to the address of the ADV_BH next-hop
- Then the 1-IX EU Route Servers advertise these prefixes
- All of the peers MUST accept /32 for IPv4 and /128 for IPv6 with BGP ADV_BH Community
- ADV_BH next-hops have unique MAC addresses in each location (determined by ARP/NDP)
- Then malicious traffic is dropped inside the 1-IX EU switching platform while legitimate traffic continues to flow
For security and stability reasons, we have currently set a limit of 50 rules per next-hop (member connection). Each community counts as a rule. For example, announcing three /32 IPv4 prefixes with two communities each counts as six rules. You don’t get a warning if you exceed this limit.
Priorities are:
1. Whitelisted
2. Blacklisted
3. Shaped
Rules that exceed the limit are dropped
If you think any additional blocking rules would be useful, don’t hesitate to reach out to us at abh@1-iх.eu - your feedback helps us improve the service.
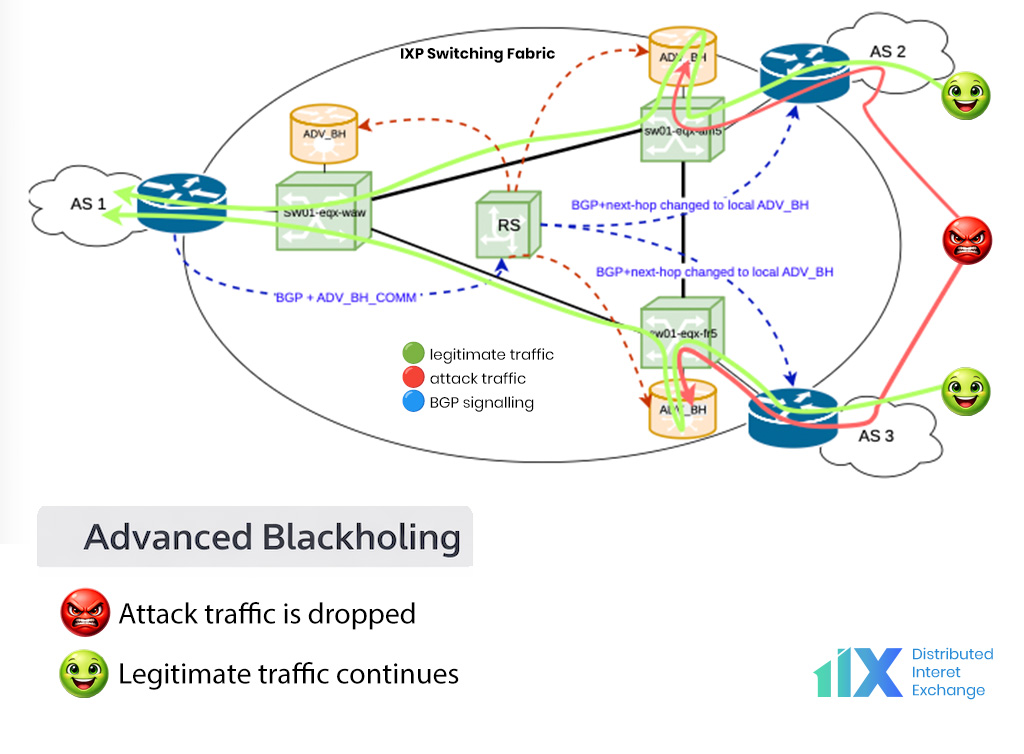
Table of Rules
| Rule | Drop Community | Shape Community | Whitelist Community |
|---|---|---|---|
| All traffic | RT:50263:4200000000 | RT:50263:4200000001 | |
| UDP | RT:50263:4200000002 | RT:50263:4200000003 | RT:50263:4200001029 |
| TCP | RT:50263:4200001030 | ||
| ICMP | RT:50263:4200000048 | RT:50263:4200000049 | RT:50263:4200001026 |
| GRE | RT:50263:4200000050 | RT:50263:4200000051 | |
| UDP, source port rules | |||
| UDP, source port = 0 | RT:50263:4217000000 | RT:50263:4217100000 | RT:50263:4217200000 |
| UDP, source port = 1 | RT:50263:4217000001 | RT:50263:4217100001 | RT:50263:4217200001 |
| UDP, source port = 3 | RT:50263:4217000003 | RT:50263:4217100003 | RT:50263:4217200003 |
| UDP, source port = xx | RT:50263:42170000xx | RT:50263:42171000xx | RT:50263:42172000xx |
| UDP, source port = yyy | RT:50263:4217000yyy | RT:50263:4217100yyy | RT:50263:4217200yyy |
| UDP, source port = zzzz | RT:50263:421700zzzz | RT:50263:421710zzzz | RT:50263:421720zzzz |
| UDP, source port = 65533 | RT:50263:4217065533 | RT:50263:4217165533 | RT:50263:4217265533 |
| UDP, source port = 65534 | RT:50263:4217065534 | RT:50263:4217165534 | RT:50263:4217265534 |
| UDP, source port = 65535 | RT:50263:4217065535 | RT:50263:4217165535 | RT:50263:4217265535 |
| UDP, destination port rules | |||
| UDP, destination port = 0 | RT:50263:4217300000 | RT:50263:4217400000 | RT:50263:4217500000 |
| UDP, destination port = 1 | RT:50263:4217300001 | RT:50263:4217400001 | RT:50263:4217500001 |
| UDP, destination port = 3 | RT:50263:4217300003 | RT:50263:4217400003 | RT:50263:4217500003 |
| UDP, destination port = xx | RT:50263:42173000xx | RT:50263:42174000xx | RT:50263:42175000xx |
| UDP, destination port = yyy | RT:50263:4217300yyy | RT:50263:4217400yyy | RT:50263:4217500yyy |
| UDP, destination port = zzzz | RT:50263:421730zzzz | RT:50263:421740zzzz | RT:50263:421750zzzz |
| UDP, destination port = 65533 | RT:50263:4217365533 | RT:50263:4217465533 | RT:50263:4217565533 |
| UDP, destination port = 65534 | RT:50263:4217365534 | RT:50263:4217465534 | RT:50263:4217565534 |
| UDP, destination port = 65535 | RT:50263:4217365535 | RT:50263:4217465535 | RT:50263:4217565535 |
| TCP, source port rules | |||
| TCP, source port = 0 | RT:50263:4206000000 | RT:50263:4206100000 | RT:50263:4206200000 |
| TCP, source port = 1 | RT:50263:4206000001 | RT:50263:4206100001 | RT:50263:4206200001 |
| TCP, source port = 3 | RT:50263:4206000003 | RT:50263:4206100003 | RT:50263:4206200003 |
| TCP, source port = xx | RT:50263:42060000xx | RT:50263:42061000xx | RT:50263:42062000xx |
| TCP, source port = yyy | RT:50263:4206000yyy | RT:50263:4206100yyy | RT:50263:4206200yyy |
| TCP, source port = zzzz | RT:50263:420600zzzz | RT:50263:420610zzzz | RT:50263:420620zzzz |
| TCP, source port = 65533 | RT:50263:4206065533 | RT:50263:4206165533 | RT:50263:4206265533 |
| TCP, source port = 65534 | RT:50263:4206065534 | RT:50263:4206165534 | RT:50263:4206265534 |
| TCP, source port = 65535 | RT:50263:4206065535 | RT:50263:4206165535 | RT:50263:4206265535 |
| TCP, destination port rules | |||
| TCP, destination port = 0 | RT:50263:4206300000 | RT:50263:4206400000 | RT:50263:4206500000 |
| TCP, destination port = 1 | RT:50263:4206300001 | RT:50263:4206400001 | RT:50263:4206500001 |
| TCP, destination port = 3 | RT:50263:4206300003 | RT:50263:4206400003 | RT:50263:4206500003 |
| TCP, destination port = xx | RT:50263:42063000xx | RT:50263:42064000xx | RT:50263:42065000xx |
| TCP, destination port = yyy | RT:50263:4206300yyy | RT:50263:4206400yyy | RT:50263:4206500yyy |
| TCP, destination port = zzzz | RT:50263:420630zzzz | RT:50263:420640zzzz | RT:50263:420650zzzz |
| TCP, destination port = 65533 | RT:50263:4206365533 | RT:50263:4206465533 | RT:50263:4206565533 |
| TCP, destination port = 65534 | RT:50263:4206365534 | RT:50263:4206465534 | RT:50263:4206565534 |
| TCP, destination port = 65535 | RT:50263:4206365535 | RT:50263:4206465535 | RT:50263:4206565535 |